P2P botnet Kelihos.B with 100.000 nodes sinkholed
Revision as of 05:26, 12 August 2015 by Eric.freyssinet (talk | contribs) (Text replacement - "p2p" to "P2P")
(Publication) Google search: [1]
| P2P botnet Kelihos.B with 100.000 nodes sinkholed | |
|---|---|
| |
| Botnet | Kelihos |
| Malware | Kelihos.B |
| Botnet/malware group | |
| Exploit kits | |
| Services | |
| Feature | |
| Distribution vector | |
| Target | |
| Origin | |
| Campaign | |
| Operation/Working group | |
| Vulnerability | |
| CCProtocol | |
| Date | 2012 / 28 mars 2012 |
| Editor/Conference | |
| Link | http://blog.crowdstrike.com/2012/03/P2P-botnet-kelihosb-with-100000-nodes.html blog.crowdstrike.com (blog.crowdstrike.com Archive copy) |
| Author | Tillmann Werner |
| Type | |
Abstract
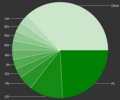
“ This past Wednesday, CrowdStrike has teamed up with security experts from Dell SecureWorks, the Honeynet Project and Kaspersky to take out a peer-to-peer botnet which we believe is the newest offspring of a family that has been around since 2007: Kelihos.B, a successor of Kelihos, Waledac and the Storm Worm. Traditionally, the botnets in this family are known for spamming, but the newest version is also capable of stealing bitcoin wallets from infected computers. There is an infographic at the bottom of this post that contains the most important facts and numbers at one glance.
Bibtex
@misc{Lua error: Cannot create process: proc_open(/dev/null): failed to open stream: Operation not permitted2012BFR963,
editor = {},
author = {Tillmann Werner},
title = {P2P botnet Kelihos.B with 100.000 nodes sinkholed},
date = {29},
month = Mar,
year = {2012},
howpublished = {\url{http://blog.crowdstrike.com/2012/03/P2P-botnet-kelihosb-with-100000-nodes.html blog.crowdstrike.com}},
}